Secure new revenue from Microsoft Sentinel customers with LogLocker
Add a new solution to your service offering, one that solves the challenge of retaining the high-value logs needed for compliance, simply and cost-effectively.
.png)
Engage customers with these resources

- One-page product introduction: A brief introduction to LogLocker's benefits to customers, partner benefits and target industries and organisations. Download the one-page product introduction PDF
- Seller guide: For use by sales and marketing people, this PDF provides information about LogLocker's value proposition, customer benefits, use cases, features, and ideal customers. Download the two-page seller guide PDF
- Pitch deck: Use these slides in presentations and sales pitches to communicate the value and functionality of LogLocker. Download the 5-page pitch deck PowerPoint slides
- Contact details: Who to contact for product, marketing, sales and general support. Download the contact details PDF
- Deployment pre-requisites guide. The elements that need to be in place before a deployment date can be confirmed. Download the deployment pre-requisites guide
LogLocker solves compliance challenges by providing a robust log management platform for the data and AI economy
- Reduced costs. Compliance teams can retain log data for the long term at a fraction of the cost of traditional archive solutions.
- Minimised data. Only archive and retain the specific logs needed for business requirements and compliance.
- Preserved logs. Retain and protect logs using blockchain technology for truly defensible legal evidence.
Reduce cost
Are your clients shocked at the limited options and long-term cost of retaining logs? Help them deploy a cost-effective alternative to Log Analytics and Azure Data Explorer archiving.
Minimise data
Compliance teams are looking for ways to avoid storing all logs. With LogLocker, they only archive and retain the specific logs they need for business requirements and compliance.
Preserve logs
Are your clients worried their logs are not given enough protection? They can now reserve and protect logs using LogLocker's distributed ledger technology for truly defensible legal evidence.
Ready for integration
LogLocker API's were designed for easy and effective integrations with Microsoft Sentinel, Log Analytics, Azure Data Explorer and other Microsoft services.
No retraining
LogLocker uses Kusto Query Language (KQL) to define the targeted log collections via Azure Sentinel allowing it to align to existing staff roles and skills.
Extensible data sources
Need to bring in other data sources? No problem. LogLocker will work with any volume or type of data, log or query.
Where is LogLocker installed?
Installed on Azure
LogLocker is deployed into any Azure subscription so your client can govern the security and location of data using the configuration option provided. Includes Terraform, Kubernetes, Storage and Logic App.
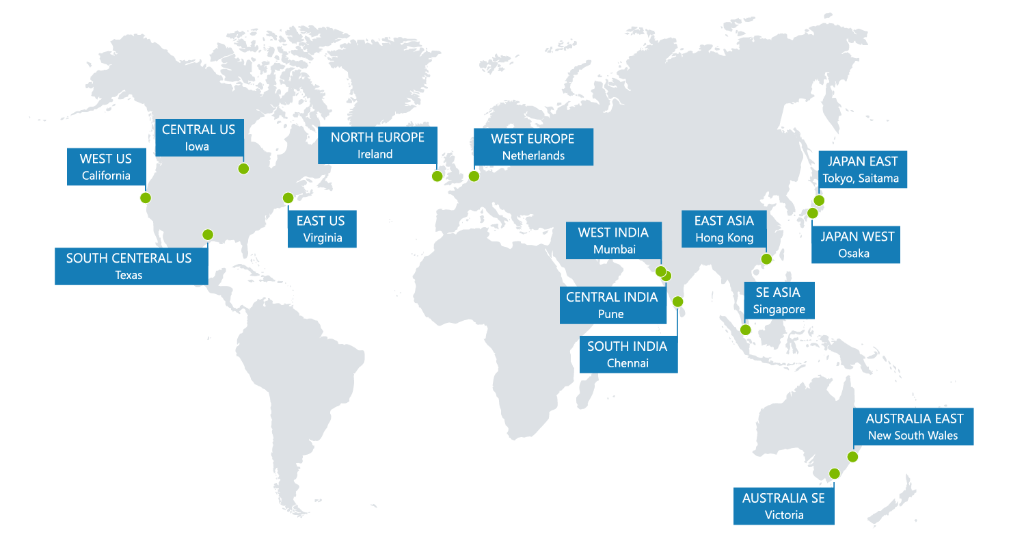
In any Azure region
LogLocker can be deployed into any Azure region ensuring clients' data is stored on the blockchain network that respects their data sovereignty requirements

Azure Blob storage options
Larger data sets can extend to off-chain storage using Azure Blob storage. Further options for multi cloud storage are also available.
How does LogLocker work?
Targeted protection
LogLocker targets the specific logs a client needs to capture using KQL queries run from Sentinel against Log Analytics and Azure Data Explorer. The LogLocker automation is then simply added to the query workbook.

Sentinel triggers
When a Sentinel alert is triggered, LogLocker will request the KQL and run the specific query against either the Log Analytics Sentinel workspace or Azure Data Explorer (ADX).
Stored logs
Only the logs a customer specifies are stored and preserved in LogLocker, ready for easy search, sharing and review.
Business
from $2850/mo
Best for smaller log volumes. Allows a customer to retain and manage high-value logs quickly and easily
-
Single tenant
-
Sentinel connector
-
Private blockchain
-
On-chain storage
-
Elastic search
Enterprise
from $5200/mo
All the Business plan features plus off-chain storage for larger log volumes
-
Single tenant
-
Sentinel connector
-
Private blockchain
-
On-chain storage
-
Elastic search
-
Azure Off-chain storage
-
ADX search
Premium
from $8350/mo
All the Business and Enterprise features plus API integration and 3rd party data sharing
-
Single tenant
-
Sentinel connector
-
Private blockchain
-
On-chain storage
-
Elastic search
-
Azure Off-chain storage
-
ADX search
-
Public blockchain options
-
AWS & GCP Off-chain storage options
-
API Access
-
3rd party permissioned data sharing
LogLocker is easy to deploy - with experts on hand to help
Azure users with a Sentinel subscription can easily implement LogLocker.
Once a client is committed to buying here's what happens next:
- They book an installation call with our engineering team
- Or, if there are immediate questions, a call with one of our team can be booked ahead of the installation meeting.
- Full details of prerequisites are provided ahead of the installation meeting.
- The LogLocker installation is completed within 5-working days once meetings are confirmed and pre-requisites are in place

Logs are ever more critical for digital compliance and security
-
Increasing cyber security costs
-
Streamlining security and compliance teams
-
Retention of high value logs for long periods
-
Increasing volumes of telemetry data
Your clients want ways to do more with less and drive value from existing security investments
Your customers' investments in SIEM (Security Information and Event Management) are likely significant. To truly reap the benefits of SIEM, they need to be sure that their security and compliance teams are getting the most value out of this powerful tool. Imagine a Venn diagram where the circles of security and compliance overlap. The sweet spot in that overlap is where SIEM should reside. This is where it becomes more than a tool—it transforms into a bridge, uniting these typically isolated areas to unveil insights and boost efficiency. By working together with LogLocker, security and compliance teams can turn SIEM into a valuable asset that shields an organisation from cyber threats and regulatory pitfalls.
Your clients need to avoid siloed teams by reusing skills, data and functionality
The disconnect between siloed security and compliance teams creates a critical blind spot. Security, focused on real-time threats, overlooks long-term compliance gaps. Compliance, chained to checklists, misses dynamic security risks. This double vision leaves vulnerabilities unseen and unaddressed, potentially increasing audit time and fines and ultimately weakening overall defence. Breaking down these silos and forging a shared view through integrated tools and proactive collaboration is key to achieving resilient security and seamless compliance.
Native options are not suitable for long-term log retention - they are costly, unable to accommodate custom data types and lack effective preservation capabilities
Safeguarding information against the relentless march of time is a complex juggling act demanding constant vigilance and resourcefulness. Storage technology constantly evolves, demanding data migration to survive, while physical media degrades, necessitating backups and redundancy measures. Data formats and software compatibility become obsolete, requiring costly conversions to maintain accessibility. Privacy concerns escalate with lengthy retention, demanding meticulous access control and potential anonymisation. The sheer volume of data can become unwieldy, requiring efficient archiving and retrieval strategies.
Your customers need tools to enable selection and filtering of logs to ensure that only those with value are processed and retained. Retaining unfiltered logs is not a sustainable option given data growth and increased regulatory requirements.
The deluge of log data threatens to engulf organisations like a rising tide. Each click, sensor ping, and system event spills into the reservoir, and the torrent shows no signs of slowing. Existing tools strain under the pressure, buckling under the ever-growing weight of analysis and storage demands. Future projections paint an even bleaker picture, with data volumes set to explode exponentially. This tsunami of information threatens to drown your customers' ability to identify critical security events and maintain regulatory compliance. Navigating this data deluge requires innovative solutions, from intelligent filtering and compression techniques to scalable storage architectures and AI-powered analysis tools. Only by riding this wave of data, not succumbing to it, can you help your customers unlock the valuable insights hidden within.